Account Data Review – 8888708842, 3317586838, 3519371931, Dtyrjy, 3792753351
Account data review for IDs 8888708842, 3317586838, 3519371931, Dtyrjy, and 3792753351 requires a structured, policy-driven approach. Identity and access legitimacy must be verified, and baseline behaviors cross-checked with real-time anomaly signals. Documentation should capture data accuracy, governance controls, and audit trails, supported by modular checks and clear thresholds. Emphasis on least-privilege access and continuous monitoring will frame actionable outcomes, enabling rapid risk response while preserving user autonomy within repeatable playbooks. The next step presents a precise workflow to implement.
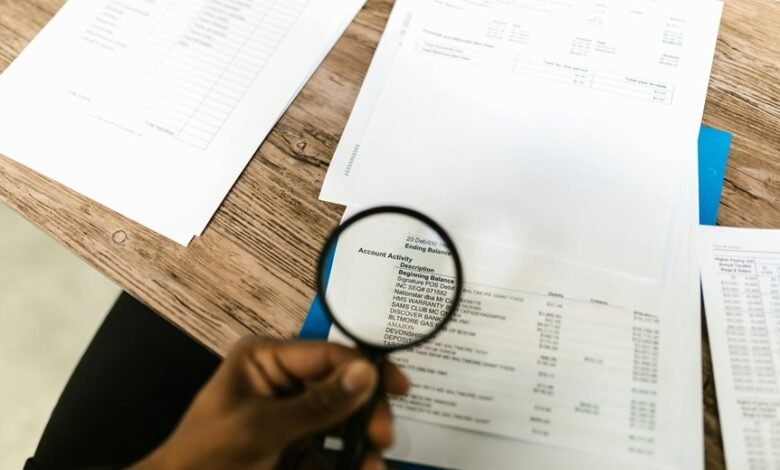
What Is Account Data Review, and Why It Matters
Account Data Review is the systematic process of examining account records to verify accuracy, detect anomalies, and ensure compliance with defined policies. It evaluates data integrity and governance, enabling informed decisions. The practice emphasizes identity verification and monitoring risk indicators, confirming legitimate access and activity. This disciplined approach strengthens control, reduce exposure, and support proactive safeguards while preserving user autonomy and operational freedom.
How to Detect Anomalies in Critical Identifiers
Anomaly detection in critical identifiers requires a structured approach that flags deviations from expected patterns in real time. The method relies on baseline behavior, continuous monitoring, and alert thresholds to identify irregularities without overreacting. Analysts interpret signals, validate sources, and isolate potential risks. Effective anomaly detection prioritizes critical identifiers, maintains transparency, and supports rapid decision-making within freedom-minded, procedural safeguards.
Step-by-Step Verification Workflows You Can Implement
Step-by-step verification workflows provide a structured template for confirming data integrity and authorization across account identifiers. They enable disciplined account review, data verification, and anomaly detection through modular checks, cross-verification, and audit trails.
The approach supports timely compliance audits, triggers investigations, and documents outcomes with clear, actionable evidence, fostering transparent independence while preserving user autonomy and operational flexibility.
Best Practices for Security, Compliance, and Trust
In an era of escalating threats, organizations must implement concrete, repeatable controls to sustain security, compliance, and trust.
The guidance emphasizes account data review as a core discipline, aligning governance with risk management and audit readiness.
Security best practices center on least privilege, continuous monitoring, and clear incident playbooks, ensuring enduring resilience while supporting autonomy and informed decision-making across teams.
Frequently Asked Questions
How Often Should I Re-Validate User Account Data?
The practitioner states: revalidation cadence should be established per risk and data criticality, balancing operational burden with data freshness. Regular checks ensure data freshness while maintaining compliance, adapting intervals as policies evolve and threat landscapes change.
Can I Automate Anomaly Alerts Across Multiple IDS?
Automation alerts can be implemented; Cross id correlation enables centralized anomaly detection across multiple ids. The system maintains independent baselines, triggers thresholds, and logs events, while remaining vigilant and unobtrusive to users seeking freedom.
What Are Common Pitfalls in Data Reconciliation?
Data quality concerns illuminate reconciliation risks, guiding governance and data lineage practices. Coincidence governs vigilance: discrepancies trigger procedural checks, cross-validation, and documentation. The approach remains concise, ensuring freedom while maintaining rigorous, repeatable data reconciliation discipline.
How Do I Measure Data Quality Impact on Trust?
Data quality directly influences trust; monitoring trust metrics requires data governance, regular validation frequency, and transparent reporting. The method measures how improved data quality shifts stakeholder confidence, ensuring procedures remain vigilant while preserving organizational freedom and accountability.
What Data Retention Policies Apply to Account Identifiers?
From a guarded vantage, data retention for account identifiers hinges on data minimization and consent management policies; organizations should limit storage, define retention periods, and document justified purposes, ensuring consented use, archivable records, and timely deletion where appropriate.
Conclusion
In a data fortress, gates hum with monitored consent and log trails like quiet lanterns along a corridor. Verification steps align the map with reality, while anomaly detectors watch as sentries across thresholds. Each identity, bounded by least-privilege keys, moves only where permitted, leaving footprints that reconcile with baselines. Real-time flags rise like glints on steel, prompting swift action. The review closes, doors left ajar to safe, auditable continuity, ready for the next measured breach of risk.




