Account Data Review – 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, e5b1h1k
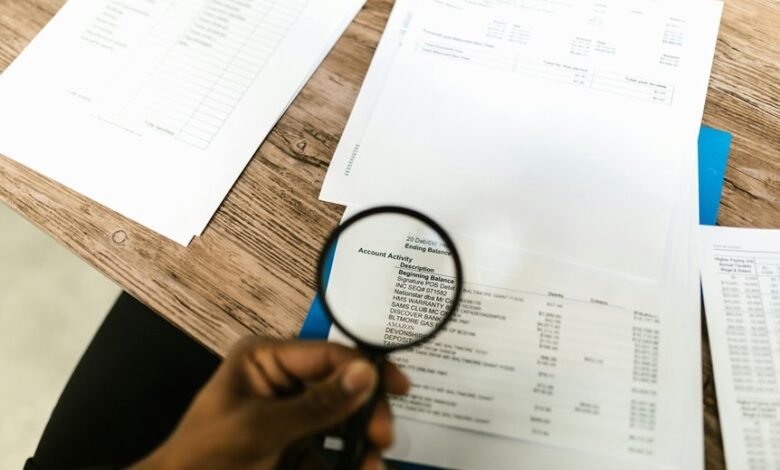
The account data review for 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, and e5b1h1k presents a structured examination of identifiers, ownership, and governance. The analysis aims to confirm accuracy, trace data lineage, and expose control points. It highlights potential inconsistencies and compliance gaps that require remediation. Stakeholders are left with unanswered questions about accountability, data privacy, and alignment with regulations, signaling where targeted validation should begin.
What an Account Data Review Is and Why It Matters
An Account Data Review is a structured evaluation of a company’s financial and operational records to verify accuracy, completeness, and compliance. This process clarifies data lineage and control points, enabling accountability and continuous improvement. It emphasizes account data privacy and data governance, ensuring sensitive information is protected while governance frameworks align with regulatory expectations, risk appetite, and strategic decision-making.
Identifying Key Identifiers and Shared Ownership
Identifying key identifiers and shared ownership is a foundational step in ensuring data traceability and accountability within an organization.
The analysis centers on delineating account identifiers and establishing clear ownership mapping to prevent ambiguity.
This approach supports governance, access control, and audit readiness, enabling independent verification, minimize risk, and promote responsible data stewardship across teams and systems.
Practical Validation Methods for 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, e5b1h1k
Practical validation methods for 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, and e5b1h1k focus on confirming identity integrity, ownership mapping, and data lineage through targeted checks, reconciliation, and auditable procedures. The approach emphasizes identifying anomalies and validating ownership via deterministic verifications, cross-system reconciliation, and traceable records, enabling transparent accountability while preserving autonomy and freedom in data governance and access controls.
Detecting Inconsistencies, Risks, and Compliance Gaps
Detecting inconsistencies, risks, and compliance gaps requires a disciplined, evidence-driven approach that quantifies deviations between expected and actual data states.
The evaluation isolates anomaly patterns, assigns objective severity, and maps control effectiveness.
Inconsistency risks are prioritized by impact and frequency, while compliance gaps reveal where policy, procedure, or governance fails.
Clear remediation plans and measurable targets ensure accountable, freedom-supporting oversight.
Frequently Asked Questions
How Is User Consent Documented During Data Review?
Consent is documented via formal consent logging, recording user approvals with timestamps, roles, and data scopes. Data privacy protocols require verification of opt-in statuses, retention schedules, and audit trails to ensure accountability during data review.
What Are Common Data Mapping Pitfalls to Avoid?
Common pitfalls, Data mapping can impede accuracy and compliance when mappings are ambiguous, omissions occur, or lineage is unclear; inconsistent terminologies, missing metadata, and over-customization complicate traceability, governance, and cross-system interoperability, undermining data quality and strategic insight.
How Often Should These Review Cycles Occur?
“Time is money,” notes suggest review cadence should be quarterly or biannual depending on risk. The data governance framework mandates timely Compliance touchpoints; reviews align with policy changes, data sensitivity, and evolving regulatory requirements, ensuring sustainable governance and accountability.
Which Stakeholders Must Review Critical Findings?
Critical findings are reviewed by key stakeholders: senior leadership, data owners, compliance, security, and risk managers. Stakeholder responsibilities are defined, and the decision making hierarchy guides escalation, approval, and remediation actions with documented accountability and traceable timelines.
How Should Misattributions Be Corrected and Tracked?
Coincidence underscores how misattribution correction procedures rely on transparent records and periodic audits; misattribution correction and attribution tracking are essential. The third party notes systematic checks, documenting sources, timestamps, and responsible reviewers for accountable, freedom-respecting governance.
Conclusion
The account data review reveals a precise map of identifiers, ownership, and governance, exposing clear lines of accountability. Despite meticulous checks, minor data drift highlights a higher risk of misalignment across systems, underscoring the need for ongoing reconciliation. The findings underscore robust controls but reveal gaps that demand remediation plans and measurable targets. If addressed promptly, the governance framework will achieve durable accuracy and transparency; otherwise, inconsistencies could balloon into systemic compliance risks—an almost cartoonishly consequential cautionary tale.





