Digital Activity Documentation Linked to 66.29.129.121 and Alerts Logs
Digital activity documentation associated with the IP address 66.29.129.121 serves as a vital component in modern cybersecurity frameworks. By systematically logging activities, organizations can identify unauthorized access attempts and other irregularities. This process not only enhances threat detection but also fortifies operational integrity. Understanding the types of alerts generated and their implications raises questions about the effectiveness of current monitoring practices. What additional measures could be implemented to strengthen security further?
Overview of IP Address 66.29.129.121
The IP address 66.29.129.121 serves as a unique identifier for devices connected to the internet, facilitating the routing of data across networks.
Its significance lies not only in enabling communication but also in revealing geographic location, which can inform various analyses.
Understanding this IP address is crucial for users seeking autonomy in navigating their digital environments and safeguarding their online presence.
Types of Alerts Generated From Activity Logs
Monitoring digital activity through logs generates various alerts that play a pivotal role in maintaining security and operational integrity.
These alerts can be categorized based on severity and type, allowing for effective log interpretation. Common alert types include unauthorized access attempts, data exfiltration signals, and system anomalies, each serving to inform stakeholders of potential risks and ensuring proactive measures are enacted to safeguard systems.
Analyzing Suspicious Behavior and Potential Threats
While organizations strive to maintain robust security protocols, analyzing suspicious behavior within digital activity logs is essential for identifying potential threats.
By examining suspicious patterns in data, security teams enhance threat detection capabilities, allowing them to proactively address vulnerabilities.
This analytical approach enables the recognition of anomalies that could signify malicious intent, ultimately safeguarding organizational assets and ensuring operational integrity in an increasingly complex digital landscape.
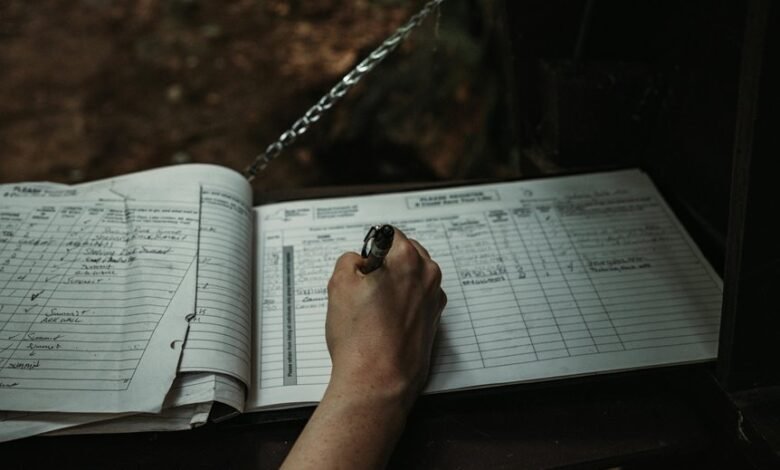
Best Practices for Monitoring and Documentation
Effective monitoring and documentation practices are vital for any organization aiming to safeguard its digital infrastructure.
Implementing robust activity tracking mechanisms enhances the ability to identify anomalies swiftly.
Employing comprehensive documentation strategies ensures that all data is accurately recorded, facilitating analysis and response.
Organizations should regularly review these practices to adapt to evolving threats, thereby maintaining control and fostering a secure digital environment.
Conclusion
In conclusion, the meticulous documentation of digital activity linked to IP address 66.29.129.121 serves as a vigilant sentinel in the realm of cybersecurity. By generating actionable alerts and analyzing potential threats, organizations can fortify their defenses against unauthorized access. Adopting best practices for monitoring not only enhances security but also cultivates a culture of awareness, transforming potential vulnerabilities into robust shields. Thus, the proactive management of activity logs emerges as a cornerstone for safeguarding digital integrity.




