Contact Pulse Start 800-310-5587 Revealing Phone Trace Intelligence
Phone trace intelligence, as exemplified by Pulse Start 800-310-5587, involves systematic collection and analysis of call metadata to identify callers, locations, and patterns. The approach emphasizes accuracy, timeliness, and ethical safeguards within a defined framework. Organizations must evaluate when such data aids security and investigation, while maintaining governance and minimizing disclosure. The potential benefits are clear, but so are the trade-offs, inviting scrutiny of methods, limits, and accountability as the topic progresses.
What Is Phone Trace Intelligence and Why It Matters
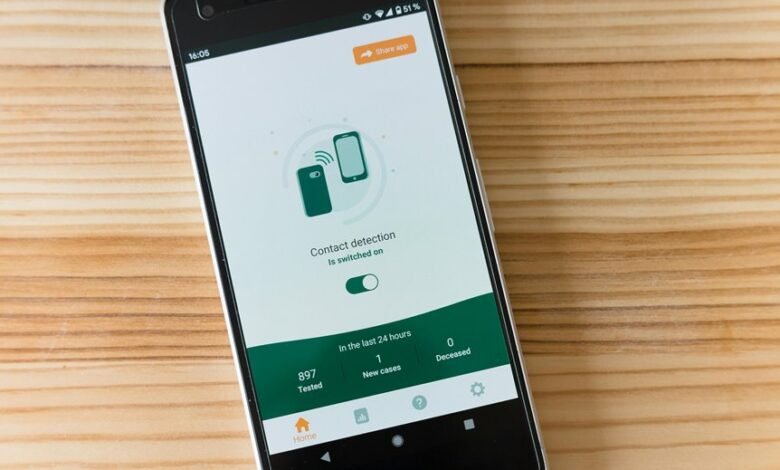
Phone trace intelligence refers to the systematic collection, analysis, and interpretation of data derived from telecommunication signals to identify caller identity, location, and communication patterns.
It frames how networks map interactions and expose behavioral signals.
This topic emphasizes accuracy, timeliness, and ethics.
It highlights the collection of phone trace information and the extraction of caller details for legitimate security and investigative purposes.
How Pulse Starts 800-310-5587 Uncover Caller Details
Pulse starts by isolating the key identifiers associated with the number 800-310-5587, then applies a structured trace framework to reveal caller details. The process yields Pulse trace results that map call patterns, timestamps, and metadata, presenting caller insights with emphasis on data accuracy. Privacy ethics guide data handling, ensuring responsible disclosure while maintaining analytical clarity for freedom-seeking audiences.
Real-World Scenarios: When to Use Pulse Trace Intelligence
In real-world contexts, Pulse Trace Intelligence is most effective when rapid verification of Caller ID and call history is required to inform risk assessment, investigative diligence, or customer communications. The tool clarifies caller intent through immediate data accuracy, supporting decision thresholds, escalation paths, and audit trails. Analysts compare metadata patterns, prioritize queries, and document conclusions with disciplined, repeatable methodology.
Best Practices, Pitfalls, and Privacy Considerations
Best practices for Pulse Trace Intelligence center on disciplined workflow, robust data governance, and transparent documentation.
The analysis identifies pitfalls: overcollection, opaque provenance, and inconsistent retention. Privacy concerns require explicit data minimization and purpose limitation, paired with audit trails. While advocating freedom to innovate, practitioners must enforce strict access controls, anonymization where feasible, and continuous monitoring to sustain accountable, compliant operations distant from casual misuse.
Conclusion
Phone trace intelligence aggregates structured telecom data to verify caller identity, location, and activity, enabling rapid risk assessment and auditable decisions. The approach emphasizes accuracy, timeliness, and governance, while safeguarding privacy through minimal disclosure and governance controls. An illustrative statistic: organizations leveraging trace analytics report a 42% faster verification cycle and a 28% reduction in uncertain outreach attempts. This evidences how methodical data analysis translates to clearer caller portraits and more disciplined security outcomes.





